Single Sign-On (SSO)
SSO for your Proof account lets you and all your teammates log into Proof using the credentials stored in your organization's SAML Identity Provider (IdP). Examples of IdPs include ActiveDirectory, Auth0, Google, and Okta. With SSO, account and credential management are not handled by Proof, but instead by your IdP.
Why SSO?
- Users in your organization can log into Proof without needing to enter their password every time.
- SSO is compatible with parent/child org structures, allowing you to propagate certain teams/groups to a respective child org upon SSO login.
- Streamline new user onboarding with just-in-time user provisioning (JIT provisioning). Users will be created and updated automatically when they log in through SSO, allowing you to scale your operation with Proof faster.
Notes
- Once SSO is configured, users' former Proof account passwords will no longer work, unless they are organization admins.
- Users' former Proof account usernames will no longer work if those usernames do not match existing usernames in your organization’s IDP.
- This documentation assumes that you already have a SAML Identity Provider (IdP). If you do not have a SAML IdP, you can use any IdP that supports SAML 2.0 such as ActiveDirectory, Auth0, Google, and Okta.
- This documentation assumes you are on a "Pro" pricing tier. See our pricing page for more details.
Configuring SSO
Service Provider (SP) Configuration
To configure SSO on your Proof account, you'll need to provide Proof with the following information from your IdP:
- Entity ID
- Target URL
- X509 client certificate
You can enter these parameters individually, or provide a metadata file or metadata URL.
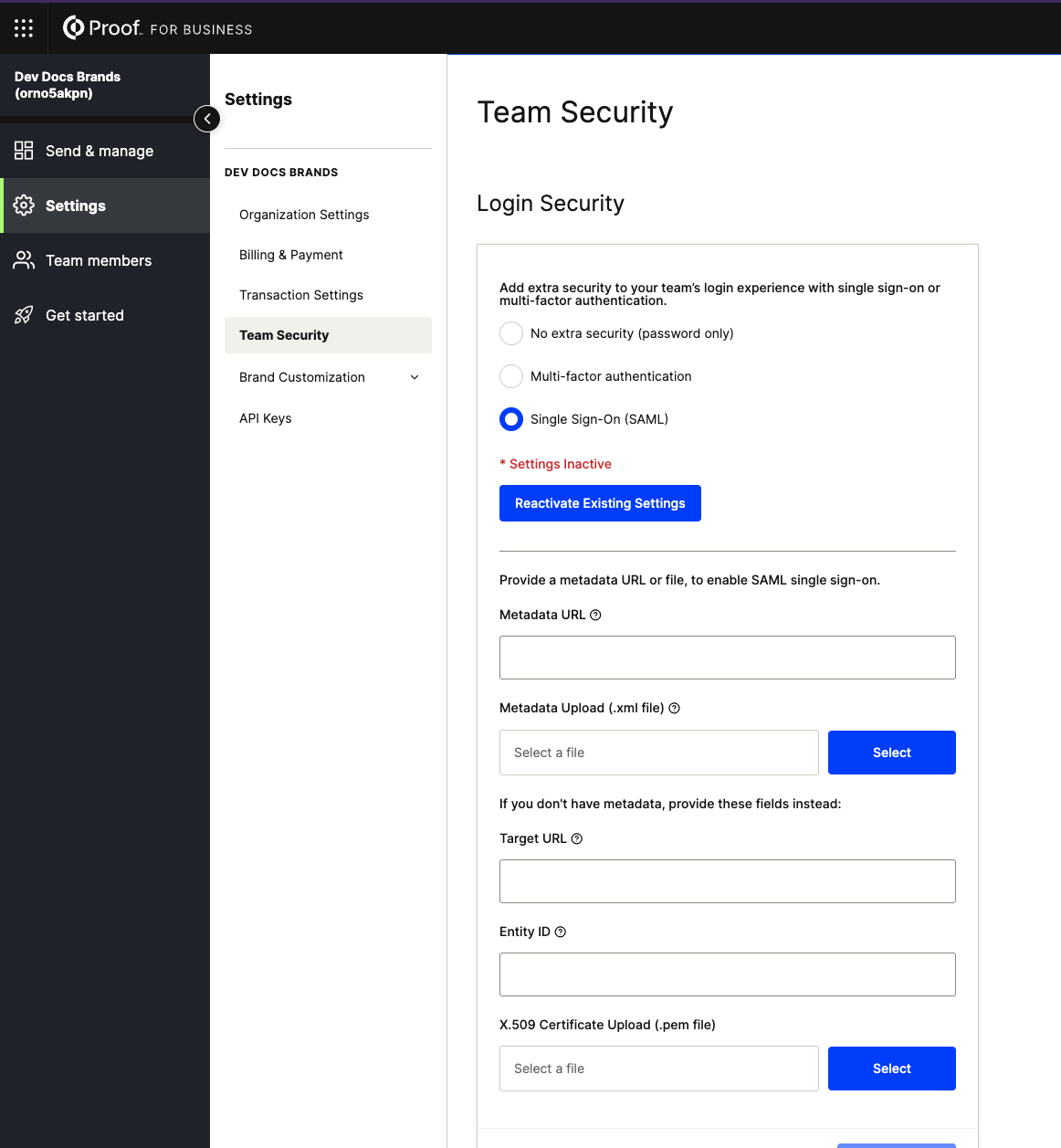
An organization admin can enable SSO and enter this information in Settings >> Team Security:
Production IdP Configuration
The IdP needs to be configured with the following Proof SAML data:
- Entity (or Issuer) ID: https://api.proof.com/saml/consume
- Assertion Consumer Service (ACS) URL: https://api.proof.com/saml/consume
- SP metadata URL: https://api.proof.com/saml/metadata
- Also available as a file
Fairfax (Test) IdP Configuration
The IdP test environment needs to be configured with the following Proof SAML data:
- Entity (or Issuer) ID: https://api.fairfax.proof.com/saml/consume
- Assertion Consumer Service (ACS) URL: https://api.fairfax.proof.com/saml/consume
- SP metadata URL: https://api.fairfax.proof.com/saml/metadata
- Also available as a file
SAML Attributes
These attributes are sent from the IdP to Proof, in order to provision accounts on-the-fly, assign specific roles (e.g. admin vs. team member), and create users in child organizations.
Keep in mind the following required attributes:
nameidfirst_namelast_nameemailroles(strongly recommended)
Read more about the available SAML attributes below:
| Attribute Name | Attribute key case | Attribute value case | Attribute Description |
|---|---|---|---|
nameid (required) | case sensitive | case sensitive | A unique, immutable identifier for the user. Can be an ID number, email address, username, etc. |
first_name (required) | case insensitive, with/without _ | case sensitive | User's first name |
middle_name (optional) | case insensitive, with/without _ | case sensitive | User's middle name. Strongly reccomended if your organization users will be signing documents in a notarization transaction. |
last_name (required) | case insensitive, with/without _ | case sensitive | User's last name |
name (optional) | case sensitive | case sensitive | User’s full name, e.g. “John Patrick Smith Jr.” |
email (required) | case insensitive | case insensitive | User's email address |
roles (strongly recommended) | case sensitive | case insensitive | An array of strings designating the user's roles. Choose any subset of the following: - admin will make the user an admin- employee will make the user a team member- notary will make that user an in-house notary for that organizationIf omitted, the default role of employee will be assigned to the user. This applies to existing users as well (i.e. an Admin user would lose their admin privileges if admin is not specified for them). |
organization_id (optional) | case sensitive | case sensitive | A Proof organization ID. If specified, the user will be added to this org, otherwise they'll be added to the org where SSO was configured. Use this attribute if you'd like to sign a user into a specific child org. |
notary_state (optional, but required if roles includes notary. | case sensitive | case insensitive | The notary’s state of operation, as an abbreviation.AZ or az |
notary_languages (optional, but required if roles includes notary. | case sensitive | case insensitive | An array of strings representing languages spoken by the user (notary). Supported values are en and es.e.g. [en], [en, es] |
Updated 7 months ago