API Keys and Authentication
All access to Proof API endpoints require an API key for authentication. Read to see how you can create and use an API key.
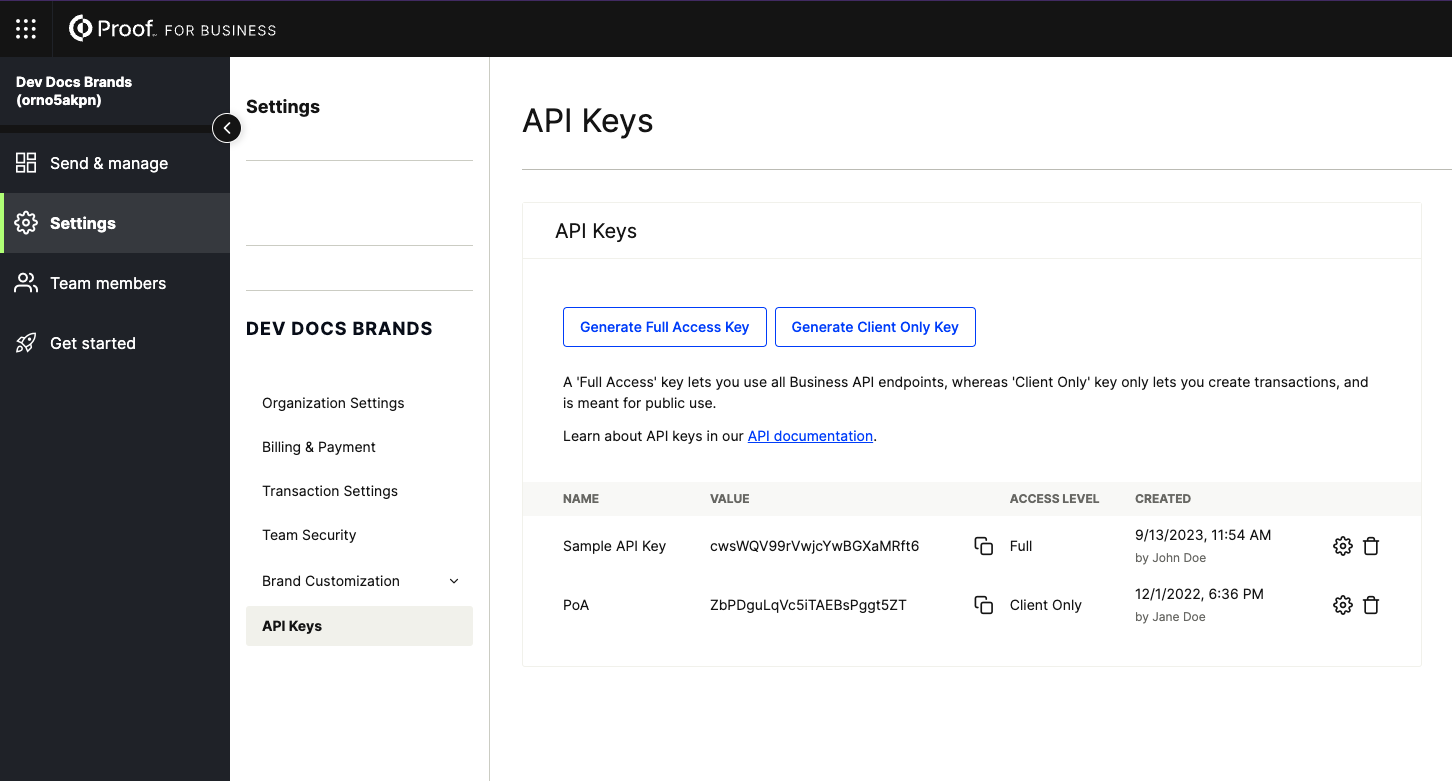
Creating a Production API Key
API Keys can be created instantly from Settings >> API Keys in your Business Account. The Settings menu is only accessible to users with the Admin role.
If you're unable to find API key settings in your account, you may need to upgrade your plan. Reach out to [email protected], or your dedicated Customer Success Manager.
Creating a Fairfax (Test) API Key
Follow the same instructions for creating a production API key, but in your Fairfax account. To gain access to our Fairfax environment, contact [email protected], or your dedicated Customer Success Manager.
Once you have access to Fairfax, creating the API key follows the same process as above for Production.
Types of API Keys
- Full Access: lets the caller create, update, and delete transactions. Meant to be secret and for internal code usage only.
- Client Only: only lets the caller create transactions. Intended for usage in client-facing applications, and thus can be freely exposed. EasyLinks are centered on Client-Only API Keys.
Authenticating via API key
Authentication is simple - just include your key in the request header with the following format:
Headers {
ApiKey: {YOUR API KEY HERE}
Content-Type: application/json
}
Updated 7 months ago